Death by Wall. The Saint Valentine's Day Massacre
February 14, 1929 was a splendid day for romantic partners to show their appreciation for each other and celebrate the special occasion of Valentine’s Day. For seven individuals, however, their destiny called for demise during the event known as the Saint Valentine’s Day Massacre in Lincoln Park, Chicago. The men gathered at a garage to wait for a scheduled shipment of Canadian whisky (Mason and Mason 146). Suddenly, four men entered the building, two dressed as police officers, and yelled at the men to get against the wall (O’Brien). Suspecting no foul play, the men did as they were told. They assumed this was another police raid in which the only harm done to them would be some jail time (“The St. Valentine’s Day Massacre”). Oh how wrong they were. Once turned against the wall, the men were filled with lead until they fell to the ground. This gruesome event caught the attention of everyone inside and outside of Chicago. The question became, who would do such an act and kill that many individuals? The answer: ‘Scarface’ Alphonse Gabriel Capone and ‘Machine Gun’ Jack Mcgurn. Their connections to the many individuals involved in the crime, as well as a solid motive, puts them as the prime suspects of the crime.
The first person of interest that irreversibly ties Capone to the crime is Jack Mcgurn who initially planted the idea of the massacre. Jack Mcgurn was a well-known bodyguard of Capone. During his time he was ordered and took out the murder of over 22 individuals, some of whom were trying to execute a bounty on Capone. Mcgurn had exquisite self-initiative being a competent boxer, professional golfer, regularly exercised, and exquisitely groomed (Burbank). However, a henchman has little reason to go against or subterfuge the orders of their boss, since it would end in their destruction . Mcgurn, before the massacre, had many attempts against his life by members of the North Side Gang, specifically by the Gusenberg brothers Frank and Peter. Both of whom were victims of the massacre. When he was asked in his hospital bed if he knew who the perpetrators were he responded with “Of course I know who shot me…When I’m well again, I’ll settle this thing myself” (Mcgurn qtd. In Burbank). Wanting revenge for his attacks Mcgurn petitioned Capone. If one of Capon’s most trusted bodyguards, someone responsible for protecting his life, wanted someone gone then Capone would have little reason to decline. If someone was trying to attack his bodyguard then they are one step closer to killing Capone.
The second item that ties Capone to this event is his vehement rivalry with George Clarence “Bugs” Moran. Bugs Morman’s North Side Gang was the direct competition to Al Capone’s South Side Gang in the smuggling industry of Chicago (“The St. Valentine’s Day Massacre’’). The competition was so intense that the North Side Gang emptied a massive amount of ammunition onto the Hawthorne Hotel on September 20th, 1926 with the intent of either killing or scaring Capone (“The Hawthorne Hotel”). This attack was in line with mobsters at the time: “Murder was deemed necessary for syndicate bosses to end competition and keep control of money flowing from their rackets, to avenge hits by rival gangs, or to prevent a hoodlum or civilian from cooperating with the police and courts” (Burbank). Capone not only had some form of grudge on his mind from previous attacks but had an incentive to kill Morman. To get rid of Morman would give a great hit to the North Side Gang’s efficiency and operation. In essence, take out the queen, and the hive crumbles. Once the gang was less of a threat this would give more operation and henceforth more profit towards Capone. Ironically, the main shipment that the men were picking up before the massacre was a hijacked container of Capone’s whisky (Mason and Mason 146). Moran was the intended target for the massacre but he missed the attack because he was running late (“The St. Valentine’s Day Massacre”). After the event when Morna was interviewed his predominant statement was “only Capone kills like that” (“St. Valentine’s Day Massacre”) which puts more bearing on Capone being the chief executor of the event. If Moran had been killed during the massacre, as intended, then Capone would have greatly benefited.
The third vital person that ties Capone to the crime is Fred “Killer” Burke. Burke had a long history of criminal activity, carrying out his first crime at the age of 17 (“Fred Burke”). Taking on many past killing contracts Burke not only had a disregard for killing but could do it on command. During the massacre, one of the primary weapons the men were shot with was a Thompson submachine gun [Tommy gun]. With recent developments in ballistic forensics, guns were finally able to be attached to the bullet of a crime. On December 14, 1929, during a raid on Burke’s house two Tommy guns were taken from Burke’s home that matched the bullets from the massacre (“The St. Valentine’s Day Massacre”). This means that Burke was part of the attack since he has the exact guns that were directly involved in the crime. Burke would not have carried out the act himself because he was lower down the ladder to Capone. Burke was just another henchman like Mcgurn meaning that Capone was above Burke giving the actual orders.
Jack Mcgurn being killed gives more of a reason as to why Mcgurn and Capone were part of the massacre. On February 15, 1936, seven years and one day after the massacre Mcgurn was shot at point-blank range in the middle of a bowling alley (“The St. Valentine’s Day Massacre”). The note left for him before the alley was raided read “You’ve lost your job; you’ve lost your dough; Your jewels and cars and handsome houses! But things could still be worse, you know…At least you haven’t lost your trousers!” (qtd. in Burbank). This card’s context was meant to have...
The Paradox of NFTs
NFTs in their current iteration are meant to solve the unique problem on the internet of personal property ownership.
“What’s an NFT? NFT stands for non-fungible token. Non-fungible is an economic term that you could use to describe things like your furniture, a song file, or your computer. These things are not interchangeable for other items because they have unique properties” (“Non-fungible tokens (NFT)” NP).
Whereas in real life an item can not be copied without strenuous effort, on the internet, obtaining a copy of that “cool new picture John Doe took of his cat” is as simple as one right click. This creates a potential dilemma, as anyone could claim to be the originator of the cat picture on the Internet, and as the image spreads of the originator’s work, it would bring exposure to the false originator. The proof of ownership dilemma has been most prevalent when trying to find the original creator of a meme - a modified image, .gif file, or video that is meant to spread a humorous idea (Myers NP). Current research has been looking outside of this limited application to see what else NFTs could be capable of. While NFTs may seem like the path to a ‘Web 3.0’ they are not a viable technology because of their current limitations. This includes their in-ability to hold large quantities of data on-chain for permanence, scale with an increasing number of transactions, and work within a centralized system.
The most current implementation of NFTs is with original artwork, in the form of .png, .jpeg, .gif, or .mp4 files, being sold on an Etsy-like visual storefront called an NFT marketplace. With the most popular market place to list these digital artworks being the website OpenSea. The concept and practice is as follows: Create a unique digital item, list it on the site, a customer buys the item and then it gets transferred to them. In reality, it is not that simple. NFTs in their modern adaptation are like gold certificates: you have proof of ownership for the gold, but you don’t actually have the gold. NFTs, instead of having the underlying piece of digital property within them, contain a metadata pointer for the property. Even though the token is contained within a digital wallet, giving the proof of ownership; the item itself is not contained within the digital wallet. The problem has already been gleaned with the shutdown of Editional, an NFT creation platform, having to move ALL of their underlying data, the actual images and pictures, to OpenSea. If it were not for this business transaction, then the only way you would be able to view these files would be from a locally downloaded backup (Stuven NP). This same scare of disappearing data would occur if OpenSea itself were to shut down because the metadata used to show the files are hosted on centralized web servers (“Non Fungible Token (NFT) platforms must secure Metadata” NP). How “immutable” of a technology claiming to be censorship resistant (Cornelius 4).
There are two solutions to this problem, neither of which are satisfactory to solve the issue. One of which, called the InterPlanetary File System [IPFS], would use content identifiers to host the file on a decentralized network so the data is distributed through multiple clients leading to a longer term permanence (“How IPFS works” NP). The Achilles Heel in this idea is that, for the data to remain ‘suspended’ or ‘retained’ within the IPFS, the data in question needs to be “pinned”. Pinning an item either requires a self-hosted solution or a bought server to pin that data. Again, you get the same issue in trusting these NFT market places. If the company shuts down, then there goes the underlying mechanism that keeps your data hosted (Stuven NP). Once that item stops being pinned, it is gone for good.
Some projects, such as Autoglyphs, have tangles with putting the image itself onto the blockchain (“Autoglyphs” NP). Then you run into another drastic problem. The point of a blockchain is only to record a history of transactions, not to store a massive amount of archival data (Raghunathan NP). Trying to fit megabytes of data into a single block makes absolutely no sense since it would practically freeze the network with how long verification for a single block would take. There would need to be computers with significantly increased random access memory and processing speed for this to even be feasible.
To reduce this weight, some groups have started to experiment with the idea of ‘regenerative NFTs’, which would recreate the files from extremely compressed source data (Yevtushenko NP). Once again, there are limitations to this idea. Since the compressed files cannot inherently hold the decompression algorithm, the NFT becomes reliant on outside sources (Stuven NP). If the algorithm were to stop working with newer operating systems and all developers had abandoned the project, then the only hope for seeing the decompressed data would be for solo software developers to make updated versions of the software. That is not a stable system for something that is meant to hold an item permanently.
Outside of art tokens, NFTs have caught the attention of academic researchers for some proof-of-concept applications. One of which involves third party certifications for the agriculture sector. The issue is most seen in the wine industry where premium producers have other retailers counterfeiting their name and subsequently tarnishing their brand and quality (Dos Santos, Ricardo Borges, et al. 21: 5307). The purpose of NFTs ensures that a non-broken supply chain is used in the delivery of the product. Since “current regulatory framework is not only inadequate to the task of regulating domestic organics, but also incapable of ensuring the integrity of imported organics” (Chenglin Liu 47: 333) the need for some kind of verifiable and adaptable system to assure quality would be necessary. While the proof of concept is solid in its foundation, it forgets one of the basic limitations of blockchain: the underlying system of NFTs.
Blockchain,...
Rhetorical Analysis of Germany’s Neo-Nazis & The Far Right
Rhetorical Analysis of Germany’s Neo-Nazis & The Far Right
January 27, 1945, Auschwitz-Birkenau, Society troops enter the concentration camp to liberate the remaining prisoners still alive. Only a few days before the death count was racking higher and higher with the execution of “The Final Solution”: a panned mass murder of anyone deemed to be an inferior race. These ideas are starting to resurface with the rise of Neo-Nazis (New National Socialist) in online communities. In the film Germany’s Neo-Nazis & The Far Right, Evan Williams uses personal stories, professional interviews, and laying out documented information and news reports to show why the threat of harmful online communities is real, and the resurgence of far-right parties, should be taken seriously and the police should be doing something to counter it.
Germany’s Neo-Nazis & The Far Right documents the resurgence of Nazis in Germany. Rather than meeting in person, as was done in the 1930s and 40s, these individuals gather, meet, and communicate on the internet. Described in this film is not how people get radicalized in these digital spaces, but what they do afterward. From planned and executed shootings, practice military operations, and weapons and ammunition hoarding, the film shows not only what the people in these spaces have done but what can be done by them. Since these ideas can be spread at a click of a button, all the actions that these people were able to plan in a digital space show that they are not only a national terrorist threat to Germany but the new radicalized individuals could be a threat to their respective country. The film follows the Investigative Journalist and Correspondent Evan Williams. Through the length of the runtime, he interviews Germany’s state intelligence chief, an online extremism expert, a network investigator, and many more to provide scope to the situation and give details on specific events. Germans already know of the problem since the attacks happened in their country. Rather than being in German, this video is in English to reach a wider audience than German people. The documentary is meant to inform the rest of the world, more particularly America (the country with the largest amount of English speakers), about not only the current threat in Germany but the looming threats that might come about in their country because of the same or similar online communities.
By using many different expert interviews this film uses ethos to further push its message. The first expert brought in is Miro Dittrich. He first clarifies that these “lone wolf” attacks aren’t exactly carried out alone. That people work together to “crowdsource” ideas such as targets, weapons, and materials to create bombs. He says that German security forces have no real interest to look at the individuals communicating this information. By giving a chance for Miro Dittrich to speak on camera, it not only gives more trustworthiness to the film creator but also further informs the audience on the issues talked about in the rest of the film. Since he is an online extremism expert, he can more intricately describe the problem and make it more digestible for a common knowledge audience. The point is to show radicalization is a real thing and that German security forces should be taking a further look into the issue.
The second expert on the matter is Stephan Kramer, the state intelligence chief of Germany, who explains why taking the situation won’t change anything and adds to Evan Williams ethos. He side-steps the argument of not taking these online communities seriously by explaining how difficult it is to pinpoint certain groups. That the internet cannot be monitored completely. This shows Evan Williams taking both sides of the argument and giving more credibility to himself as an investigative journalist. Even if security agencies were to take the issue seriously, it would be extremely difficult to find the internet communities where these people reside.
The film also uses logos to further hit the nail on the head for its persuasion and argumentation. In the film there are countless photos, videos, chat records, group hierarchy, and diaries related to online “hate groups.” All the details given show how big of an issue these communities really are. There are dedicated persons’ not only documenting what they think but also publishing and sharing material to either take action now or plan for the future. All the data are meant to show examples of what the group is supposedly planning for. When they have the ability to stock over ten thousand units of weapons ammunition the question becomes: what could they continue to do without getting caught. The diaries in particular give a glimpse inside of the mind of someone who has been ingrained with a certain message and cannot be talked to. This goes back to the point of taking the issue seriously. Evan Williams has shown what measures the people within the group will go to for their ideology. Rather than standing by and waiting for the next attack, active measures should be taken for the protection of the community.
The way this documentary shows the current threat is by giving personal stories from attacks that were carried out which adds to the film’s pathos. The first story was of Stephan Balliet’s attack and followed Christina Feist and Max Privorozki’s recollection of the event. On that day Christina Feist recalls when the congregation started to read from the Torah they heard a loud bang at the door. Little did she know that was the gunshot of Balliet trying to breach the door. The film then cuts to the raw footage of Balliet attempting to breach the door with a handgun. With an immediate transition of news reporters commentating on the event saying that two people were shot near the synagogue in the east German city of Halle by Balliet. The combination of raw footage, their interviews, and news footage lets the watcher immerse themself into the events of that day. It is meant to show...
College T-shirt Tier List
Back when I was about to graduate highschool on October 21st, 2019 I saw a youtube video that was the colmination of this blog post. https://freecollegeshirts.weebly.com//>. I got them. Here was the Tier list that I made for my friends and at-least the ones I received. Arizona State Univeristy was the most generious by sending me two when I accidentally batched an email twice.
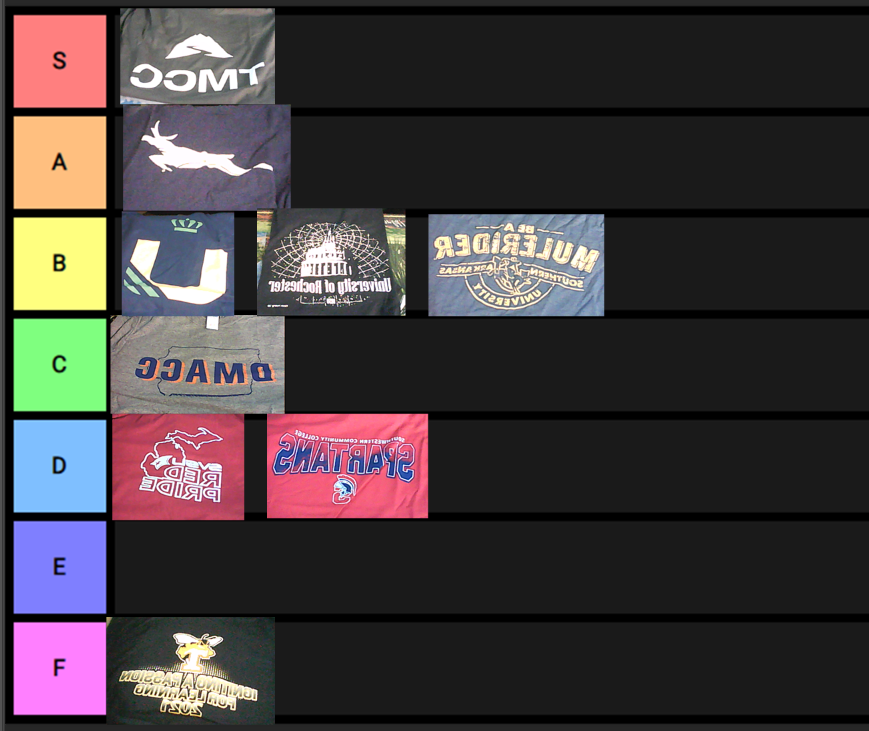
Also, for anyone who is still trying to do it today here’s the full list. I wouldn’t reccomend it for the most part as only a few shirts were actually worth it. Along with the fact that you’re less likely to receive them today due to the wave of spam back in 2020 that the colleges got. However, there are two reasons I’m posting this lis pubically
- I see this list going online for $ cost being sold to them. While it makes sense for them to be charging for collecting all the addresses into one list, for most of them the colleges/universities are public instutitons. Thereby, public information.
- For those that are in need of clothing this is one way to go about it. | ———————————————————— | —————————————– | ————————- | ——————- | | University of Alaska | admissions@alaska.edu | Anchorage | AK | | Alaska Christian College | admissions@alaska.eduedu> | Soldotna | AK | | National Park Community College | admissions@alaskacc.edu | Hot Springs National Park | AK | | University of Alaska Fairbanks | admissions@npcc.edu> | Fairbanks | AK | | University of Arkansas - Fort Smith | admissions@uaf.edudu> | Fort Smith | AK | | Alabama A&M University | admissions@uafs.eduu> | Huntville | AL | | Athens State University | admissions@aamu.eduedu> | Athens | AL | | Auburn University | admissions@athens.eduu> | Auburn | AL | | Auburn University at Montgomery | admissions@auburn.edu | Montgomery | AL | | Birmingham-Southern College | admissions@aum.eduu> | Birmingham | AL | | Calhoun Community College | admissions@bsc.edun.edu> | Decatur | AL | | Enterprise State Community College | admissions@calhoun.edu | Enterprise | AL | | Faulkner State Community College | admissions@escc.edurstate.edu> | Bay Minette | AL | | Gadsden State Community College | admissions@faulknerstate.edu> | Gadsden | AL | | Huntingdon College | admissions@gadsdenstate.edu | Montgomery | AL | | Jacksonville State University | admissions@huntingdon.edu | Jacksonville | AL | | Lurleen B. Wallace Community College | admissions@jsu.eduedu> | Andalusia | AL | | University of Montevallo | admissions@lbwcc.edulo.edu> | Montevallo | AL | | Northeast Alabama Community College | admissions@montevallo.edu | Rainsville | AL | | Northwest-Shoals Community College | admissions@nacc.edudu> | Muscle Shoals | AL | | Oakwood University | admissions@nwscc.eduedu> | Huntsville | AL | | Samford University | admissions@oakwood.eduu> | Birmingham | AL | | Southeastern Bible College | admissions@samford.edu | Birmingham | AL | | University of South Alabama | admissions@sebc.eduabama.edu> | Mobile | AL | | Trenholm State Technical College | admissions@southalabama.edudu> | Montgomery | AL | | Troy University | admissions@trenholmstate.edu | Troy | AL | | Tuskegee University | admissions@troy.edue.edu> | Tuskegee | AL | | University of Alabama | admissions@tuskegee.edu | Tuscaloosa | AL | | University of Alabama at Birmingham | admissions@ua.edudu> | Birmingham | AL | | University of Alabama in Huntsville | admissions@uab.eduu> | Huntsville | AL | | University of North Alabama | admissions@uah.eduu> | Florence | AL | | Snead State Community College | admissions@una.eduedu> | Boaz | AL | | Arkansas Northeastern College | admissions@snead.edu | Blytheville | AR | | Arkansas State University | admissions@anc.edu.edu> | Jonesboro | AR | | Arkansas Tech University | admissions@astate.edu | Russellville | AR | | Central Baptist College | admissions@atu.eduu> | Conway | AR | | Harding University | admissions@cbc.edug.edu> | Searcy | AR | | Hendrix College | admissions@harding.eduu> | Conway | AR | | Henderson State University | admissions@hendrix.edu | Arkadelphia | AR | | John Brown University | admissions@hsu.eduu> | Siloam Springs | AR | | Lyon College | admissions@jbu.edudu> | Batesville | AR | | Mid-South Community College | admissions@lyon.eduhcc.edu> | West Memphis | AR | | North Arkansas College | admissions@midsouthcc.edu | Harrison | AR | | Northwest Arkansas Community College | admissions@northark.edu | Bentonville | AR | | Northwest Technical Institute | admissions@nwacc.edu> | Springdale | AR | | Ouachita Baptist University | admissions@nwti.edu> | Arkadelphia | AR | | University of the Ozarks | admissions@obu.edu.edu> | Clarksville | AR | | Phillips Community College U of A | admissions@ozarks.edu> | Helena-West Helena | AR | | Pulaski Technical College | admissions@pccua.eduech.edu> | North Little Rock | AR | | Southern Arkansas University Magnolia | admissions@pulaskitech.edu | Magnolia | AR | | Southeast Arkansas College | admissions@saumag.edu> | Pine Bluff | AR | | University of Arkansas Community College Batesville | admissions@seark.eduu> | Batesville | AR | | University of Arkansas at Little Rock | admissions@uaccb.edu> | Little Rock | AR | | University of Arkansas for Medical Sciences | admissions@ualr.eduu> | Little Rock | AR | | University of Arkansas at Pine Bluff | admissions@uams.eduu> | Pine Bluff | AR | | University of Arkansas | admissions@uapb.eduu> | Fayetteville | AR | | University of Central Arkansas | admissions@uark.edu> | Conway | AR | | Williams Baptist College | admissions@uca.edu.edu> | Walnut Ridge | AR | | University of Arizona | admissions@wbcoll.edudu> | Tucson | AZ | | Arizona State University | admissions@arizona.edu | Tempe | AZ | | Arizona Western College | admissions@asu.eduern.edu> | Yuma | AZ | | Bryan University | admissions@azwestern.eduity.edu> | Tempe | AZ | | Central Arizona College | admissions@bryanuniversity.edu |...
Fraud Script
Joke Script for a Video I never made
I’ve have had the consumeristic need for useless stuff lately
one problem, I’m broke, and being irresponsible at the age of redacted, I don’t have any money Because of this I have decided to look up to the greatest minds in Washington (starts to print money)
Alright I just came back from Walmart. It seems as (they) though Walmart doesn’t want to accept my genius for reasons of “counterfeit” and federal crime
I think their just jealous
So that was a failed idea. On to the next. I’ve been hearing a lot of press on tax fraud lately, maybe I’ll give that a try. I’ve heard it saves you a lot of money.
It’s been a few days now and I just got a letter from the IRS. The ‘I’m really smart’ agency. It’s probably to congratulate me for my well thought out financial technique.
Ah sh*T